Preface
When it come to IR, a lot of time, you will come across some type of files that will need to be analyzed. However, the thought of having to reverse engineering malware might sounds absolutely terrifying, especially if you don’t know where to start.
In this post, I thought I’d share some resources on how I started learning malware analysis. My recommendation is to set small goals and achieve them over time. I think it took me 3 years since I first picked up Assembly to actually started using IDA and sortaaaa understand all the things.
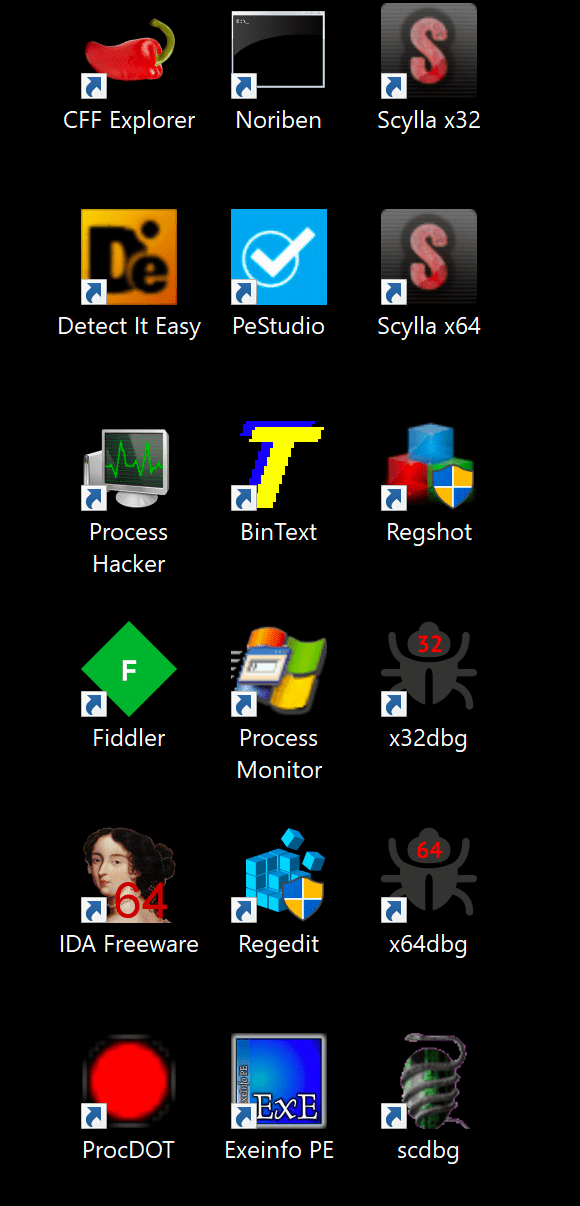
My toolset + workflow
Everyone has a workflow of how they like to begin their analysis upon receiving a sample. These are my very sort and sweet quick thinking of tools that I will want use depending on what I want to look for. But first off, make sure to have your VM set up and good to go. I have both FireEye’s Flare VM and SANS’s REMNUX VM. Both are open sourced. One is a Windows platform and the other is in Linux.
High level items
Depending on your goals with the malware, if it’s for your job as IR, then you’ll want to grab quick C2 links to identify other hosts that may potentially be infected. If it’s as a hobby, then you’ll want to dig deep inside the malware, its API/imports and all of each functions.
For this, you’ll want to answer a few quick questions, such as:
- What’s the file name?
- File size?
- File hash?
- Is it packed?
- What does it seems to do?
Quick, actionable intel are things like:
- Network connections or domain it reach out to
- Malware’s Mutex
Additional questions to answer:
- What’s the purpose of the malware?
- How’d it get here?
- Who is targeting us? How good are they?
- How can I get rid of it?
- What’d they steal?
- How long has it been here?
- Does it spread on its own?
- How can I find it on other machines?
- How do we prevent this from happening in the future?
Why analyze?
Once we’re more matured, it’ll help us to:
- Assess damage
- Discover IOCs
- Determine sophistication level of intruder
- Identify vulnerability
- Catch the “Bad guy”™
- Answer questions
Intro to malware analysis
Static analysis
AKA what information can we collect before running it
- Fingerprinting file - hash, strings, PE header..etc
- Strings, file, xxd, md5sum, etc…
-
Some info, not all. But a great place to start
Static analysis Tools
- Strings
- PeStudio
- Exeinfo PE
- CFF Explorer
- FLOSS
- Bytehist
- Detect It Easy
- BinText
Web or Javascript
- Fiddler
- Spider Monkey
Dynamic Analysis
AKA let it run, and observe in a controlled environment
Dynamic Analysis Tools
- API Monitor
- Regshot
- Process Hacker
- ProcMon
- ProcDot
- Wireshark
Automated Sandbox
These are good to keep in the back of your mind. I usually only do static analysis or put the sample in a disassembler since it’s a hobby and I don’t do this for work.
- Cuckoo’s sandbox
- Any.run
- Hybrid Analysis
- Joe’s sandbox
Disassembly + Debugger + Unpacking
If you run into a packed malware, and it wasn’t packed with popular packer such as UPX, then your best best is to run it and dump out the unpacked executable from memory.
- x64dbg
- IDA
- Scylla
- Scdbg
Where to learn malware analysis
Basics
- MalwareUnicorn’s RE101 and RE102
- Open Security Training’s Site
- 0ffset’s Blog + course
- Hasherezade’s Blog + Channel
- Dr. Fu’s Blog
- SensePost’s Crash Course in Assembly
- Infosec Institute’s Assembly Intro
- SentinnelOne’s Zero to Hero Course
Malware Network Analysis
Malicious Documents
Getting Better
- OALabs
- Colin Hardy
- Objective-See’s Mac Malware Blog
- And read as many reverse engineering tutorials as you can get your hands on
- Then try it hands on!
Great books to pick up
- Malware Analyst’s Cookbook and DVD: Tools and Techniques for Fighting Malicious Code
- Practical Malware Analysis: A Hands-On Guide to Dissecting Malicious Software
- Learning Malware Analysis: Explore the concepts, tools, and techniques to analyze and investigate Windows malware
- The IDA Pro Book: The Unofficial Guide to the World’s Most Popular Disassembler
That’s all I have for this blog. These are my favorite go to tools!